The Most Common Passwords and Why You Should Avoid Them
Every day, there are around 65,000 attempts to hack SMEs in the UK – 4,500 of which are successful. That’s approximately 1.6 million businesses per year.
33% of UK organisations claim to have lost customers after a data breach, and 45% of UK consumers claim they would stop using a business after a security breach, with 41% saying they would never return post-breach.
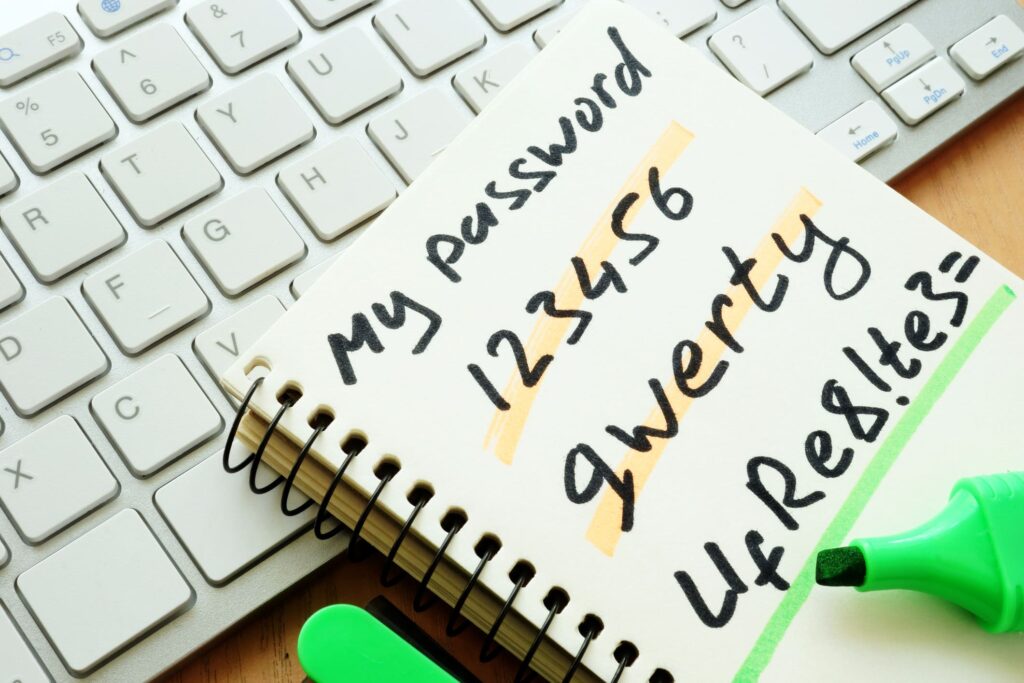
Strong, unbreakable passwords are paramount. Yet despite the data and the leaked password incidents that occur every year, many people still choose to use incredibly common passwords that are easy to guess. Here are the most common passwords that people use, and why you should avoid them at all costs.
What are The Most Common Passwords?
Each year since 2011, Internet security firm SplashData releases a list of the most common passwords that people use. The list is extrapolated from data examined from millions of leaked passwords in data breaches, mostly from North American and Western Europe.
These were the top ten most common passwords in 2019:
- 123456
- 123456789
- qwerty
- password
- 1234567
- 12345678
- 12345
- iloveyou
- 111111
Lists from previous years show that little changes. The words “password” and “qwerty” and some variation of numbers in ascending order always sit in the top spots. Other sources, such as password manager Keeper and the National Cyber Security Centre also report that these trends are present when looking at the most common passwords of people affected by data breaches.
If you’ve just seen one of your passwords present in the list above, you should seriously consider changing your password as soon as possible before you become victim to a breach.
Why are Common Passwords a Bad Idea?
Cyber-attacks are a massive threat in our ever-increasingly digital world, to both consumers and businesses. There can be catastrophic damage caused by certain sensitive information being released and stolen personal information could be used for identity theft.
When crafting passwords, they should be difficult for someone to guess. So, avoiding using any personal, easily obtainable information, like your name or the name of your pet, is crucial.
How Do Hackers Crack Passwords?
There are a number of ways a hacker might gain access to passwords, such as using a keystroke logger which records keystrokes as they’re typed, so they can see what people are using as their password. They may also exploit the vulnerabilities in a system’s password storage and find them stored somewhere on a machine with a simple search.
But for cracking passwords without obtaining them, hackers use a technique known as a Brute Force Attack. They use software that tries out tens of thousands, or even hundreds of thousands of different usernames and passwords as quickly as possible. They work by calculating every possible combination that could make up a password and testing it to see if it is correct. The longer the password, the longer it takes for the software to crack it.
Therefore, if you use a short and easy-to-guess password, for instance one random word, it won’t take very long for a hacker to crack it. And if you use this password for every site you use, including sites that have your bank account linked to them, like Amazon, then hackers who discover your password will have access to every website you use and all the sensitive data that goes with it.
How to Create a Strong Password
Aside from avoiding the most common and obvious passwords, here is some general advice for creating a secure password:
- Choose a long password, 12 characters minimum
- Include a mix of numbers, symbols, capital and lowercase letters
- Don’t use obvious dictionary words like “dog”
- Avoid common phrases or words that typically go together like, “the cat in the hat”
- Don’t use personal information that can be easily found out, like the name of your school
- Use uncommon or bizarre words in a random order
Rather than trying to think of a random phrase yourself – because people tend to be notoriously bad at this with our tendency to look for patterns – you can use online word generators to create random words that you can then put together to make a phrase.
It is recommended that you use a different password for each site you use, so that if a hacker does discover one of your passwords, they won’t automatically have access to everything else, too. It can be difficult to remember multiple passwords, but you can use tools such as a password manager, which will safely store all your passwords and is accessed with a single master password.
Make sure you never share your password with anyone, whether in person or online. If you receive an authentic-looking email from a service you use asking for your password, chances are it is probably a scam, and you should report it – and definitely do not reply with your password.
We hope that this article has helped emphasise the importance of good password practices. If your business is looking for cost effective IT support in Bedfordshire, or you would like further information on our services, please contact Tristar Tech Solutions today.